Posts tagged ‘centos’
How to Configure Sendmail & SpamAssassin for SPF Check
We had a Sendmail Server (8.14.7) running on CentOS Server, The server acts as a Secondary MX and SMART hosts for many domains. In this scenario we decided to install the SpamAssassin to force the Sendmail server to validate SPF records prior to accepting the email. I have written the below post to explain the whole process with few notes on troubleshooting I had to perform during the installation & configuration stages.
-Sendmail (already installed and running)
-SpamAssassin v. 3.4.0 (already installed with CentOS , use spamassassin -V to check the version)
– Spam-ass milter
So let’s start with the process;
+ Install spam-ass milter
# yum install perl-Mail-SPF perl-Mail-DKIM perl-Razor-Agent pyzor poppler-utils re2c ( These are the prerequisites)
# Download the RPM from https://centos.pkgs.org/7/epel-x86_64/spamass-milter-0.4.0-7.el7.x86_64.rpm.html and install by rpm -i “rpm name”
+ Start the spamassassin & spamass-milter services
# systemctl start spamassassin
# systemctl start spamass-milter.service
Now we need to force sendmail daemon to use the milter for antispam processing. Add the below lines in sendmail.mc (** do not forget to backup the files before modifying it)
======================================================================================
dnl #
dnl # SPAMASSASSIN dnl
dnl **
dnl ** enable spamassassin-milter to scan for spam using spamassassin **
dnl **
INPUT_MAIL_FILTER(`spamassassin’, `S=unix:/var/run/spamass-milter/spamass-milter.sock, F=, T=C:15m;S:4m;R:4m;E:10m’)dnl
define(`confMILTER_MACROS_CONNECT’,`t, b, j, _, {daemon_name}, {if_name}, {if_addr}’)dnl
define(`confMILTER_MACROS_HELO’,`s, {tls_version}, {cipher}, {cipher_bits}, {cert_subject}, {cert_issuer}’)dnl
dnl # END LOCAL ADDITIONS
dnl #
======================================================================================
+ save the file & quit it
+ Compile the Sendmail configuration & restart the sendmail services.
# m4 /etc/mail/sendmail.mc > /etc/mail/sendmail.cf ( or you could simply type make)
# systemctl restart sendmail
To confirm whether all these components are working fine with the relevant SPF check you need to run ,
# spamassassin -D < /usr/share/doc/spamassassin-3.4.0/sample-spam.txt 2>&1 |grep -i spf
Thereafter we could analyze whether the email are being filtered properly with the SPF Check, to check that run
# grep spf /var/log/maillog
if it is not functioning well you should look for the errors & start troubleshooting it. In my case it was throwing the below error;
“Mar 4 15:34:20 mail spamd[11685]: spf: lookup failed: addr is not a string at /usr/share/perl5/vendor_perl/IO/Socket/IP.pm line 662.”
After few minutes of googling , we found out that , it was a bug in the perl-socket module in CentOS 7 , thus you need to
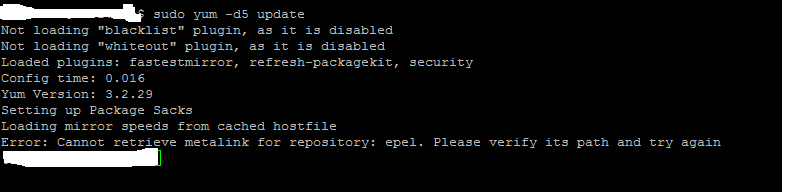
# yum install epel
# yum update perl-Socket –enablerepo=cr
You need to restart the sendmail , spamassassin & spamass-milter services for the changes to take effect and review the log again for any errors.
+ A new cron.d job will be created automatically for the spamassassin update in the /etc/cron.d/sa-update file.
Few advice, do not modify any files in /usr/share/spamassassin , since these files will be overwritten with spamassassin updates. Thus always modify the /etc/mail/local.cf for any customizations and it is a system wide configuration.
Secondly you could refer the below samples , that you could use for any customization and whitelisting stuff with in spamassassin.
========================================================================
# How many hits before a message is considered spam.
required_hits 5.0
# Text to prepend to subject if rewrite_subject is used
rewrite_header Subject [*****SPAM*****]
# Encapsulate spam in an attachment
report_safe 1
# Enable the Bayes system
use_bayes 1
# Enable Bayes auto-learning
bayes_auto_learn 1
bayes_path /home/spamd/
bayes_file_mode 0666
# Enable or disable network checks
skip_rbl_checks 0
use_razor2 0
use_dcc 0
use_pyzor 0
# Mail using languages used in these country codes will not be marked
# as being possibly spam in a foreign language.
# ok_languages all
# Mail using locales used in these country codes will not be marked
# as being possibly spam in a foreign language.
# ok_locales all
# Whitelist important senders
whitelist_from *@xyz.xx
========================================================================
That’s it , but during this process i came across useful blog sites and forums posts that helped me to work on this task and they are listed below for your reference as well.
Sendmail + SpamAssassin + SpamAss-Milter + Milter-GreyList
How to install SpamAssassin on a virtual server with CentOS 6
SPF with SpamAssassin
http://forums.sentora.org/showthread.php?tid=1118
https://it.megocollector.com/linux/install-spamassassin-on-centos-6/
http://forum.icewarp.com/forum/showthread.php?1809-Spamassassin-SPF-and-spoofing
https://centos.org/forums/viewtopic.php?t=60477
https://vamsoft.com/support/tools/spf-policy-tester (This will validate you SPF check in the email server)
http://spamassassin.1065346.n5.nabble.com/return-path-test-td1869.html
https://www.howtoforge.com/community/threads/spamassassin-version.74/
Update1:
In January 2018 , barracuda removed the RBL from the SA ruleset (it was under 72_active.cf in /usr/share/spamassassin)
To add this rule , you need to register via the below URL; http://barracudacentral.org/account/register
and then you need to manually edit the local.cf file add the below texts and restart the services
ifplugin Mail::SpamAssassin::Plugin::DNSEval
header __RCVD_IN_BRBL eval:check_rbl(‘brbl’,’bb.barracudacentral.org’)
tflags __RCVD_IN_BRBL net
header __RCVD_IN_BRBL_2 eval:check_rbl_sub(‘brbl’, ‘127.0.0.2’)
meta RCVD_IN_BRBL __RCVD_IN_BRBL_2 && !RCVD_IN_BRBL_LASTEXT
describe RCVD_IN_BRBL Received is listed in Barracuda RBL bb.barracudacentral.org
score RCVD_IN_BRBL 1.2
tflags RCVD_IN_BRBL net
header RCVD_IN_BRBL_LASTEXT
eval:check_rbl(‘brbl-lastexternal’, ‘bb.barracudacentral.org’)
describe RCVD_IN_BRBL_LASTEXT Last external is listed in Barracuda RBL bb.barracudacentral.org
score RCVD_IN_BRBL_LASTEXT 2.2
tflags RCVD_IN_BRBL_LASTEXT net
endif
Update 2:
Recently we were blacklisted by backscatter and the reason for listing was , sending out NDR for non valid emails. Thus we have add the below line in the local.cf configuration file
whitelist_bounce_relays myrelay.mydomain.net (Replace it with your outgoing email server name) If you have multiple servers , you could add them all here in multiple lines . Once the above is added and the spamassassin is restarted , issue the below command to verify for any config errors #spamassassin --lint The below URL contains additional information to test the backscatter rule via sample bounce messages. https://wiki.apache.org/spamassassin/VBounceRuleset https://forums.untangle.com/feedback/11356-backscatter-spamassassin.html
Update 3:
After some time we realized the above settings , does not fulfill our requirement and had to modify the sendmail.mc as below
Original Config
define(confPRIVACY_FLAGS',authwarnings,novrfy,noexpn,restrictqrun’)dnl
Change it to
define(confPRIVACY_FLAGS',authwarnings,nobodyreturn’)dnl#
Compile the sendmail and restart the sendmail services.
CentOS yum error 14: PCYURL ERROR 7 – “Failed to connect to 2a02:2498:1:3d:5054:ff:fed3:e9
Dear Folks
When you are trying to update the system with yum , you may come with the above error , In which the yum tool is trying to resolve the mirrorlist url’s via IPv6 Address.
![]() What happens here is that when the yum is unable to resolve and reach the IPv4 address it end up trying the IPv6.
What happens here is that when the yum is unable to resolve and reach the IPv4 address it end up trying the IPv6.
Hence if you face the similar issue , I would advice you to go through the below steps and identify the real cause.
Step 1 – Check whether you could resolve the URL (mirrorlist.centos.org) via nslookup or dig and get an IPV6 address.
If you fail at the above step check for the DNS configurations in /etc/resolv.conf
Step 2 – Check with the firewall team that they have allowed the ports 80 , 443 ,21 from the linux server.
In my case it was the firewall blockage.
I have been googling regarding the same issue and found out that several articles pointing to IPV6 saying that to disable it. Hence you could try that as a last resort , if the above steps did not succeed.
– edit the /etc/sysconfig/network and the /etc/sysconfig/network-scripts/ifcfg-eth* files to disable any entries pointing to IPv6
– edit /etc/sysctl.conf and put the below entries and reboot the server
net.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.disable_ipv6 =
– disable the ip6tables.
Good Luck